Why is it worth commissioning an IT system audit? Why should you know if you have it?
IT systems are permanently embedded in companies. If they do not work, you cannot work at all, well-implemented they allow for effective work, excellent customer service and competitive advantage. The benefits include customer satisfaction, better employee productivity that was unthinkable 10 years ago, improved profitability and better business decisions thanks to information about the company that managers can access from anywhere in the world.
These obvious advantages of a modern work environment may, however, cease to be available as a result of failures or attacks by cybercriminals. Identifying and assessing risks, and preventing these risks, is an important part of a manager's job.
To achieve maximum benefits and minimize threats, reliable information about what the company's IT system really is is essential. This knowledge allows you to make the right decisions now and plan for future development.
Many managers ask themselves the following questions:
- Could a company work more efficiently thanks to IT solutions?
- Is what I have being optimally used?
- Was the money on IT purchases well spent?
- Am I safe? Is the operation of the company at risk?
- How much should you spend to remove threats and when should it be done?
- What investments need to be made to better utilize resources? Will existing IT systems support the planned growth?
So check what you have, check your IT department or the external company that serves your company. If you contact us, we will jointly define the scope of the audit appropriate to your needs.
What are some examples of the positive impact of IT systems on business??
IT systems (technological solutions and IT infrastructure) have a huge impact on the functioning and development of business. Below are some examples of the benefits that a company can gain from a good implementation of applications working on an efficient IT system.
1. Process automation
Example: Implementing an invoice scanning and handling system enables automatic entry of invoice data into the accounting system, eliminating manual rewriting and reducing the number of errors.
Business benefit: Saving time and staff costs, fewer errors, faster payment approval.
2. Improving the quality of customer service (CRM)
Example: The use of a CRM (Customer Relationship Management) system, which collects a full history of customer contacts, allows sales and customer service departments to respond faster and propose personalized offers.
Business benefit: Increased customer satisfaction, higher cross- and upselling sales, better market relations.
3. Better decisions with data analytics (BI)
Example: Business Intelligence (BI) tools are used by companies to analyze sales, market trends, and website user behavior. Reports and dashboards allow managers to respond immediately to interest in specific products, fluctuations in demand, or changes in customer behavior.
Business benefit: Better strategic and operational decisions, better matching of the offer to market needs, maximization of profits.
4. Collaboration and communication (cloud tools)
Example: Collaboration platforms (such as Microsoft 365, Google Workspace, and Slack) enable quick access to cloud documents, real-time collaboration, and efficient communication regardless of employees' location.
Business benefit: Acceleration of information flow, greater flexibility of teams (e.g. remote work), lower office infrastructure costs.
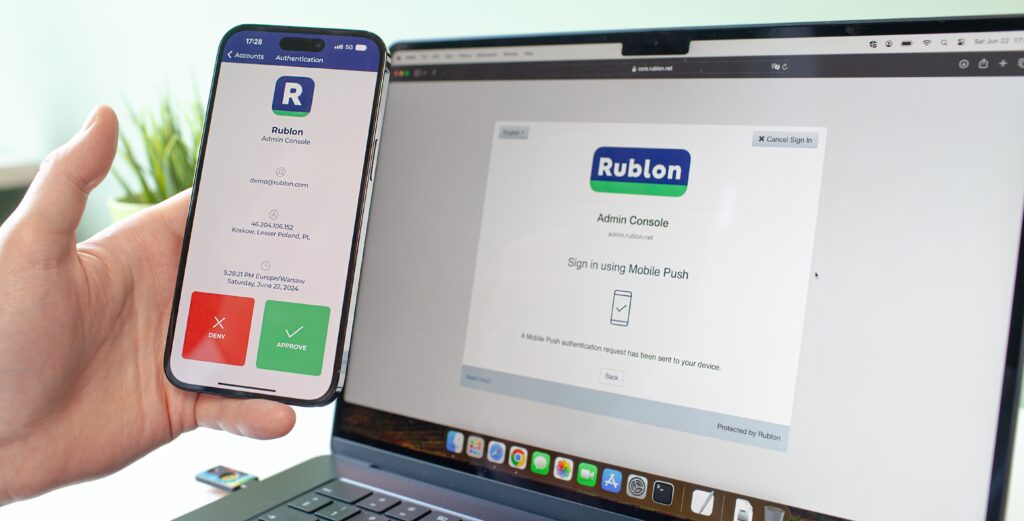
5. Data security and business continuity
Example: IT systems with backup, encryption and threat monitoring mechanisms help protect sensitive data (e.g. customer data, sensitive data, financial information) and quickly restore system operation after a failure or hacker attack.
Business benefit: Avoiding financial losses related to downtime, reducing the risk of penalties for improper data protection, maintaining customer trust.
6. Supply Chain Optimization (ERP)
Example: ERP (Enterprise Resource Planning) systems integrate production, warehouse and logistics processes, enabling, among other things, more efficient inventory planning and real-time shipment tracking.
Business benefit: Reduction of storage and transportation costs, reduction of delays, better utilization of resources (e.g. machines).
7. Increase your reach with e-commerce
Example: Launching an online store (e.g. on the Shopify platform or your own system) opens up access to new markets and enables 24-hour sales.
Business benefit: Higher revenues, the ability to acquire new customers from outside the local market, scaling the business without the need for large investments in physical infrastructure.
8. Personalization of the offer and marketing (marketing automation)
Example: A marketing automation system (e.g. HubSpot, Marketo) helps you create automated email campaigns, segment your audience, and track campaign results in real time.
Business benefit: Higher effectiveness of marketing communications, better conversion rates, automatic sending of personalized offers.
9. Increasing competitiveness
Example: A company that builds a market advantage by offering customers modern solutions (e.g. mobile applications for ordering services or fast online payments) can gain customer loyalty more quickly.
Business benefit: Greater market share, higher brand value, outpacing the competition in innovation.
Each of the above-mentioned IT solutions can bring measurable financial effects to the company (including cost reduction or increased revenues), as well as significantly strengthen its position on the market through better efficiency and increased security.
How do we collect data during an audit?
To prepare a report, we need knowledge about the company, its processes and resources. We obtain it in 3 ways.
1. Surveys – during conversations with company representatives we collect the following information:
- Management's expectations regarding the role of the IT system in the enterprise.
- General information about the IT system and its components.
- Compliance with our “Good IT System” standard.
- IT security solutions.
2. Resource inventory – using appropriate tools and upon loan of internal company documents, we will examine:
- Procedures related to information processed in IT systems.
- Installed software and compliance of the actual state with the licenses held.
- Network equipment and its configuration.
- Central resources (servers, storage, backups).
- Processed data and access rights thereto.
- User computers and peripherals.
3. Testing the resistance of IT systems to cyber threats – using specialized tools, we will perform:
- Detection of devices in the IT system (including unwanted ones).
- Vulnerability scanning.
- Phishing tests (on request).
What is included in the report?
1. General overview of the system status (Executive Summary)
- A short, understandable for non-technical readers synthesis of the most important information: whether the system is stable, what are the main challenges, key achievements and risks.
- The most important conclusions and recommendations for action.
2. Current IT infrastructure
- Description of the main infrastructure elements (servers, network, end devices, cloud systems, key business applications).
- Information about any changes in the infrastructure since the last report (new implementations, hardware replacements, updates) – if the previous report is available.
- Outline of the systems architecture from a business perspective (which systems are critical, which support individual business processes).
3. Availability and performance
- Availability (uptime) indicators of key systems and services over a given period (e.g. during the last quarter).
- Response time, application speed and possible exceedances of SLA (Service Level Agreement) standards.
- Information about outages (planned vs. unplanned downtime) – how many outages there were and how they were resolved.
4. Security and compliance
- Major security events such as detected incidents, attempted attacks, or data breaches – with a description of how they were resolved.
- Status of updates for operating systems, software, and security patches.
- Information about security tests (e.g. penetration tests) and planned corrective actions.
- Compliance with legal and regulatory requirements (e.g. GDPR, industry security standards).
5. Costs and budget
- Summary of IT costs incurred in the analyzed period (hardware, licenses, services, support costs).
- Budget utilization in relation to plan (planned vs. actual expenditure).
- Forecasted costs for the coming periods and proposed investments.
6. Incidents and Reports (Help Desk / Service Desk)
If the following data is shared, we will also describe:
- Number of tickets handled and response/resolution time.
- Recurring problems – whether modernization, additional training, hardware or software replacement is required.
- User satisfaction level (if the company conducts internal opinion research).
7. Development projects and activities
- Status of ongoing IT projects (e.g. implementation of a new ERP or CRM system, migration to the cloud, automation).
- Information about planned completion dates and resources (human, financial, equipment) necessary to complete the projects.
- Preliminary assessment of business benefits from ongoing or recently completed projects (e.g. process improvements, cost reduction, work acceleration).
8. Risks and recommendations
- Identified risks (e.g. aging infrastructure, lack of sufficient security, connection congestion, dependence on a single vendor).
- Estimated scale and likelihood of impact on business operations.
- Recommendations for risk minimization (e.g. backups in another location, additional security testing, modernization of specific elements).
- IT system development path (e.g. hybrid cloud implementation, new cybersecurity tools).
9. Strategic Summary
How the current state of the IT system supports or limits business goals.
What are the next steps to increase efficiency and safety?
Overall development forecast and the role of the IT department in implementing the company's plans.
10. Attachments and detailed data (optional).
Dictionary important for managers IT related concepts
This dictionary presents key concepts from the area of management and security in companies, including IT (Information Technology) and OT (Operational Technology) solutions. It includes definitions of systems supporting business activities (e.g. ERP, CRM, BI), mechanisms ensuring continuity of work (e.g. BIA, BCP, RPO, RTO) and threats (e.g. ransomware, hacker attack). The entries included here show how IT and OT technologies intertwine, improving not only the flow of information, but also the control of physical processes in the company. Thanks to this, you can protect resources more effectively, increase productivity and react faster to market changes.
Process automation (process automation) is the use of technology and software to streamline repetitive tasks and procedures in a company. Thanks to this, the company can operate faster, cheaper and with less risk of human error. At the same time, employees gain more time for tasks that require creativity and decision-making.
E-commerce (e-commerce) is a way of buying and selling products or services on the Internet. It allows customers to make purchases from anywhere and at any time, and allows companies to reach a larger audience. This allows for increasing sales reach, speeding up transactions and improving convenience for both sellers and buyers.
Marketing Automation (andautomation of processes in marketing) is the use of tools and software that independently perform repetitive tasks, such as sending mailings, publishing content or customer segmentation. This makes it easier to reach recipients with the right message at the right time, which increases the effectiveness of the campaign. Marketing employees gain time to plan strategies and create more creative activities.
EOD (Electronic Document Circulation) is a system that allows you to process company documents in digital form instead of paper. This allows for faster distribution of information, better version control and automation of acceptance processes. Such a system not only makes it easier to search for archived documents, but also supports cost savings and an ecological work model.
UC&C (Unified Communications & Collaboration) that is, sGroupware systems are tools that facilitate collaboration between team members regardless of where they are located. They enable document sharing, real-time communication, and task coordination in one place. As a result, the company operates more efficiently, and decisions can be made faster and more effectively. An example of a collaboration environment is Microsoft 365, i.e. email, document libraries, and Teams.
ERP (Enterprise Resource Planning) is an integrated software that helps manage key areas of the company, such as finance, sales, warehouse or human resources. Thanks to it, all data and processes are in one place, which facilitates cost control and better resource planning. As a result, the company can make faster decisions and respond more efficiently to market changes. Examples of ERP systems include Comarch XL, Comarch Optima, Microsoft Dynamics, Exact
CRM (Customer Relationship Management) is a system that helps a company manage customer relationships in terms of marketing, sales, customer service and board of directors. It makes it easy to track contact history, save purchase information and preferences, so the company can better understand customer needs. As a result, you can more effectively tailor offers and provide higher quality service. Examples of CRM systems include ZOHO, Salesforce, Dymamics 365.
BI (Business Intelligence) is a way to transform company data from various systems into useful information that helps in making business decisions. By using analytical tools and clear visualizations, managers can quickly spot trends or emerging problems. This allows them to act based on hard data, instead of just relying on intuition.
Ransomware is malware that locks or encrypts company data and then demands a ransom to restore access. Criminals often infect systems through infected email attachments or malicious links. As a result, a company can become inoperable if it does not have an effective security plan and backups. More information on this topic in the article RANSOMWARE – HOW TO BEHAVE WHEN WE ARE ATTACKED AND HOW TO PROTECT OURSELVES TO MAINTAIN THE CONTINUITY OF BUSINESS PROCESSES on our blog.
Hacker attack is an unauthorized action that aims to breach the security of a system or network in order to steal data, disrupt operations, or perform other harmful activities. Hackers often exploit software vulnerabilities, lack of employee awareness, or social engineering methods. This can lead to the loss of confidential information, financial losses, and damage to the company's image.
BIA (Business Impact Analysis) is the process of identifying and assessing which areas of a company are most vulnerable to the effects of downtime or failure. This allows you to set priorities in protecting key assets and business processes to minimize financial and reputational losses. In this way, the company gains the knowledge necessary to prepare effective contingency plans and maintain business continuity.
BCP (Business Continuity Plan) is a plan that describes how a company should proceed in a crisis situation so as not to interrupt key activities. It contains procedures and resources needed to restore the most important processes in the shortest possible time, e.g. after a system failure or other unexpected event. Thanks to it, the company minimizes losses and returns to normal functioning faster.
RPO (Recovery Point Objective) is the maximum amount of time back that a company can afford to lose data in the event of a failure or other event. Determining the RPO helps determine the appropriate frequency of backups and how to restore them. This allows the company to know to what point in the past it must go back with data to return to normal operations as quickly as possible.
RTO (Recovery Time Objective) is the maximum time a company can afford to have key systems or processes down after a failure. Determining RTO helps determine how quickly a company should restore operations to avoid significant losses or downtime. This allows you to plan appropriate actions, resources, and emergency procedures that will ensure rapid recovery of business continuity. You can say that this is the time needed to restore a company's systems to the RPO point.
IT (Information Technology) is a field that covers the use of computers, software, and networks to process and transmit information. It includes both hardware and systems, as well as services that enable the automation of business processes, communication, and data storage. Thanks to IT, companies can operate more efficiently, develop faster, and better respond to customer needs.
OT (Operational Technology) are technologies and systems used to monitor and control processes in industry and other areas where the continuity of operation of machines and infrastructure is key. Unlike IT systems, they focus mainly on the physical world, supervising production, energy or transport. Thanks to OT, companies can work safely and efficiently, minimizing the risk of equipment failure.
If you are interested in our services, please contact us by phone:
or using the form -> Contact | Upgreat